Google’s Android is rated as one of the most popular mobile operating systems across the globe and will account for almost half the worldwide smartphone sales by the end of 2012, as predicted by Gartner.
Popularity
Although there are several reasons for the popularity of this operating system, for customers there are two main things that affect their buying decision. First, Android is open source and for making devices based on this operating system manufacturers have to pay a fraction of what they used to pay OS providers earlier. Second and most important, the large number of applications available on Android Market makes a huge impact on buyers’ minds.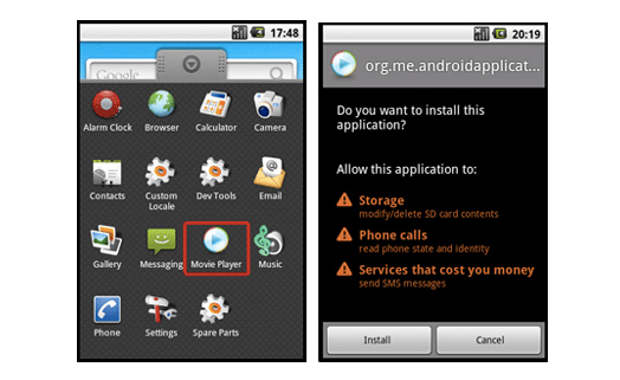
Also, being an open source OS, Android attracts a lot of independent developers and programmers who contribute towards the development and improvement of Android as an operating system with inputs for the OS as well as for applications.
With the increase in popularity and adoption by a significant number of users globally, Android has turned into a breeding ground for threats coming from hackers and Virus makers who tend to benefit from the popularity of Android.
###PAGE###
The threat
Since smartphones have replaced computers and notebooks to a great extent and are capable of monetary transaction and online purchases, hackers are turning their attention to grabbing confidential financial data from users using Android smartphones.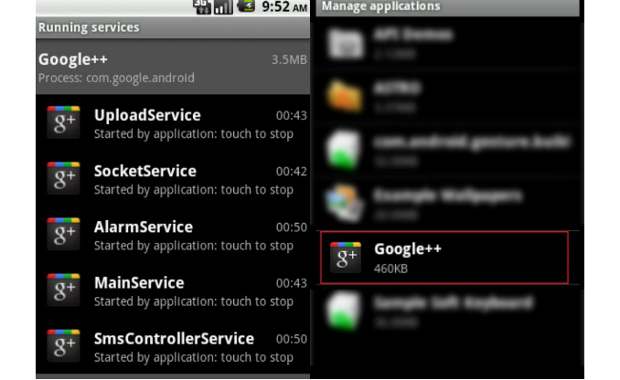
According to Panda labs’ quarterly threat report 2011, “Android is becoming the dominant platform of mobile computing and is likely to win the tablet market shortly. Additionally, there is increasing concern about cell phone security, and research studies and proof of concepts reporting security problems have multiplied over the last few months.”
“Cyber-crooks are beginning to realize the existence of an emerging market they are willing to exploit, and are trying new techniques while continuing to use proven strategies, like using malware to get infected phones to send SMS text messages to premium rate numbers.”
A recent security threat that has been identified on Android is a Trojan or malicious program disguised as an application, and it is found to record conversations.
“As the application market continues to boom, users should be more cautious that they know what they’re installing,” said Lawrence Pingree, a Gartner analyst. “For example, they should only install applications from trusted sources and ensure that permissions match up with the respective application’s core features. Anti-malware protection will also go a long way in helping to ensure the user’s mobile device has the latest protection.”
###PAGE###
Security measures
Due to a large number of free applications, people have started trying out new apps by the dozen. Users get apps and uninstall them if they aren’t useful. Iit isn’t worth people’s time to read each app’s privacy policy. Many applications aren’t malicious per se but are very intrusive and expose the phone to threats that are malicious. If users were more careful of what they’re loading on their device and the permissions it demands, a large part of the security problem would cease to exist.
Google too takes measures to minimize threats by implementing programs like Google Bouncer. Once an application is uploaded to Android Market, Bouncer starts analyzing it for known malware, spyware and trojans. It also looks for behaviors that indicate an application might be misbehaving, and compares it against previously analyzed apps to detect possible red flags. While both new and old applications are scanned only older applications are tested for potential threats to Android users. The program runs every application on Google’s cloud infrastructure and simulates how it will run on an Android device to look for hidden, malicious behavior.
###PAGE###
The remedy
Android smartphone users need to be careful while using their devices. They need to think particularly before tapping on unknown links. And they need to make sure they read all the information and check the authenticity of the application. 
“First of all there are simple things to know when using a smartphone. If you’re installing an app, it shouldn’t be asking for permission to access the nooks of your Android. You should download apps directly from the native Market, and it’s always better to first check user-generated ratings there. It will give you an idea about the quality of the App and its troubles. So just think for two minutes, not one, before downloading and installing an app. Also be careful about allowing escalated privileges to the app, read the pop-ups instead of just clicking along until it installs,” suggests Pankaj Jain, spokesperson of ESET India, a company that develops security solutions.
Along with that, simple things like installing applications as far as possible from a reputed or official application store can be exercised by users to stay protected, even though they might not get the particular application they desire.
Also, installing an antivirus program helps a great deal. The antivirus program constantly monitors the device for suspicious activity and upon detection can remove or at least block the application from executing certain actions, thereby safeguarding users.


