After WannaCry, another ransomware attack is wreaking havoc across the world. Many organisations in Europe, US and India have been infected by a new ransomware attack dubbed as “Petya”.
The worst hit nation is Ukraine where many government sites, Ukranian National Bank, and some power companies are crippled by the latest attack. In India, Jawaharlal Nehru Port (JNPT), country’s largest container port, has been hit by the cyber attack. The government said that one of the terminals at the JNPT port has been impacted by the malware attack. “The (shipping) ministry has confirmed that one terminal at JNPT has been affected due to the attack at Maersk’s Hague office,” an official said to PTI.
Danish transport and energy firm Maersk is also affected by the malware attack and it said in a statement on its site which reads, “We can confirm that Maersk IT systems are down across multiple sites and business units due to a cyber attack.” In addition, Russian energy giant Rosneft said on Twitter that it was facing a “powerful hacker attack.”
What is Petya ransomware attack?
Before starting with the Petya ransomware attack, let’s us first know what a ransomware actually means. Through this technique, hackers hold your computer hostage by encrypting almost all the data on your device until you pay the ransom amount asked by the hacker. The hackers give you a limited time to pay the ransom, or else they will wipe out the entire data.
Petya is a form of a virus, which was spotted by many security firms in the past. The ransomware uses the similar loophole found in Windows, which WannaCry used to carry out a massive attack. Recently in April, a hacker group known as Shadow Brokers leaked tools known as EternalBlue.
How is it different from WannaCry?
Unlike WannaCry, Petya basically locks down computer’s hard drive as well as individual files stored in it. This makes it harder to recover the information from the computers that are affected by this ransomware.
How does it work?
According to Juniper, the malware does not just encrypt files on a targeted system one by one – it also encrypts the hard drive’s master file table (MFT) which renders the master boot record (MBR) useless and the system unable to boot.
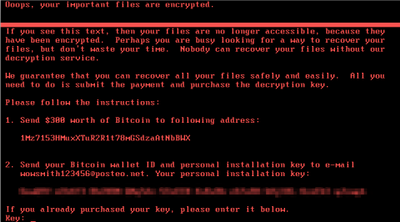
The malware then reboots the infected system and once it is done, it shows displays a fake message and secretly encrypts the whole system. The firm further states that the Petya ransomware has actually replaced the system’s MBR with custom malicious code that displays a ransom note, leaving the device unable to start. The attacker then asks for $300 worth of bitcoins in exchange for the decryption key.
How do I protect myself?
Sadly, there is no fix available at the moment to stop this ransomware attack. But many cybersecurity experts believe that one should immediately backup all the data on an external drive. In case you are hit by the ransomware, switch off the computer the moment you see this image and don’t turn it on.
.png)
Interestingly, many experts believe that wiping your machine and restoring your data from backups is one way to recover from this attack. However, if you do not do regular updates and sadly, there is nothing one can do.


