India’s cyber security agency the Indian Computer Emergency Response Team (CERT-IN) has issued a new threat alert for Android users in the country this week. It says that a new vulnerability is capable of letting attackers infect your device with malware-laden apps, and you won’t even come to know about it. ” An Elevation of Privilege vulnerability named “StrandHogg 2.0” had been reported in the Google Android due to confused deputy flaw in the “start activities()” in the “ActivityStartController.java” which allow the attacker to hijack any app on an infected device,” the CERT-IN advisory mentioned.
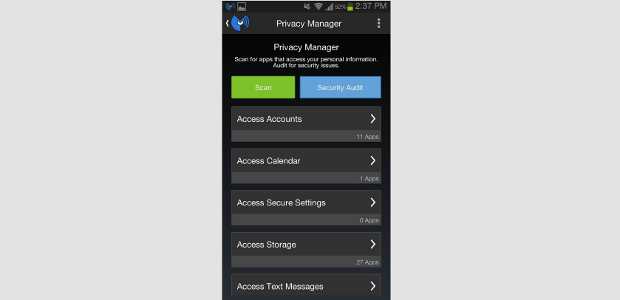
Using this vulnerability, attackers can discreetly infect your device with malware with apps that look genuine. And if you activate the malware/app, chances are they can access and control any app on your phone. Once that happens, the security agency says, the victim’s phone contact, photos and even messages can be read and sent by that person.
“Successful exploitation of this vulnerability could allow the attacker to gain access to a victim’s login credentials, SMS messages, photos, phone conversations, spy on the user through the phone’s microphone and camera and also track GPS location details on an affected device,” the advisory highlighted the concerns.
It also points out the theStrandHogg 2.0 affects Android phones that are running on versions between Android 9 (Pie) and Android 3 (Honeycomb). Considering Android 10 doesn’t have a huge software share in the ecosystem, this vulnerability can easily impact more than 80 percent of Android devices in the country. Industry report says Android runs on more than 95 percent of phones in the country, which invariably makes it a hotbed for hackers, who can easily circumvent through security holes like these.
Which is why it’s important for all handset makers to upgrade their devices to Android 10, as many as possible. We’re hoping that CERT-In warning would have been sounded out to all device manufacturers in the country, who can then look to fix the issue.
For users, they are advised to not install apps from third-party app store (no guarantee of app security there) and click on download files from mails sent by unknown sources. CERT-In has been proactive about such issues in the past few months, and we’re hopeful those alerts are taken seriously and acted upon.